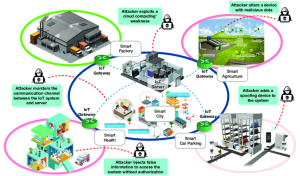
It is a relatively new term in hacking, but it’s gaining popularity. A vulnerability assessment is done by gathering information about the system. To do this, the hacker gains access to the system’s network. A vulnerability assessment and penetration testing singapore aim to find vulnerabilities in your target. After finding them, they’re then exploited using various tools. This could mean scanning ports, looking at running services, taking snapshots of files, trying to guess passwords, etc. These techniques are often referred to as ‘penetration tests.’
Vulnerabilities Assessment
It’s performed to identify the vulnerabilities of a system. Different types of vulnerabilities can be linked. These include software security excrescencies, network security issues, physical security, stoner authentication, and digital storehouse bias. Once these vulnerabilities have been linked, they need to be fixed. It should be done periodically to identify changes in the system.
- It is performed at any time previous to system perpetration. In addition to performing original threat analysis, the findings may lead to identifying implicit issues that could be addressed before deployment. This could mean that the threat mitigation plan is streamlined.
- It helps to identify security conditions that weren’t preliminarily linked. These conditions may have been overlooked due to a lack of training or experience.
- It helps IT staff members understand their druggies’ terrain and how they interact with it. As a result, they can make informed opinions about what systems should be installed and configured.
- It provides information regarding user behavior and access rights. This helps IT staff determine if there is a need to restrict specific types of users from accessing certain applications or data.
Penetration Testing
Penetration testing (pen testing) examines computer networks, systems, operations, and data. A pen tester attempts to compromise information security by testing for sins in the perpetration and design of those rudiments. Pen testers use technical tools and ways to test for vulnerabilities and attempt to exploit them.
- Penetration tests are performed after a vulnerability discovery is linked. They’re used to assess the inflexibility of the discovered issue further.
- Pen-testers give sapience into the internal workings of a network. They use various tools and styles to gain access to systems and networks.
- Penetration testers can perform tasks that other testers cannot. They can gather data from inside a network, look for sins in firewalls, and collect information that a regular tester would not have access to.





More Stories
Efficient Content Saving: Keeping Facebook Media Ready for Offline Viewing Anytime
Cost efficient security approaches maximizing coverage while minimizing ongoing monitoring expenses
Personalized Care Solutions Powered By Adaptive Software Patient Centered Analytics